Diabetes Life Home Overview
The Diabetes Life home page is where practical guidance meets independent evaluation. We publish plain-language reviews and how-tos that help readers sort through products, tools, and services related to diabetes management, digital privacy, and everyday digital life. Our mission is to present clear, actionable information that you can apply without pressure to buy.
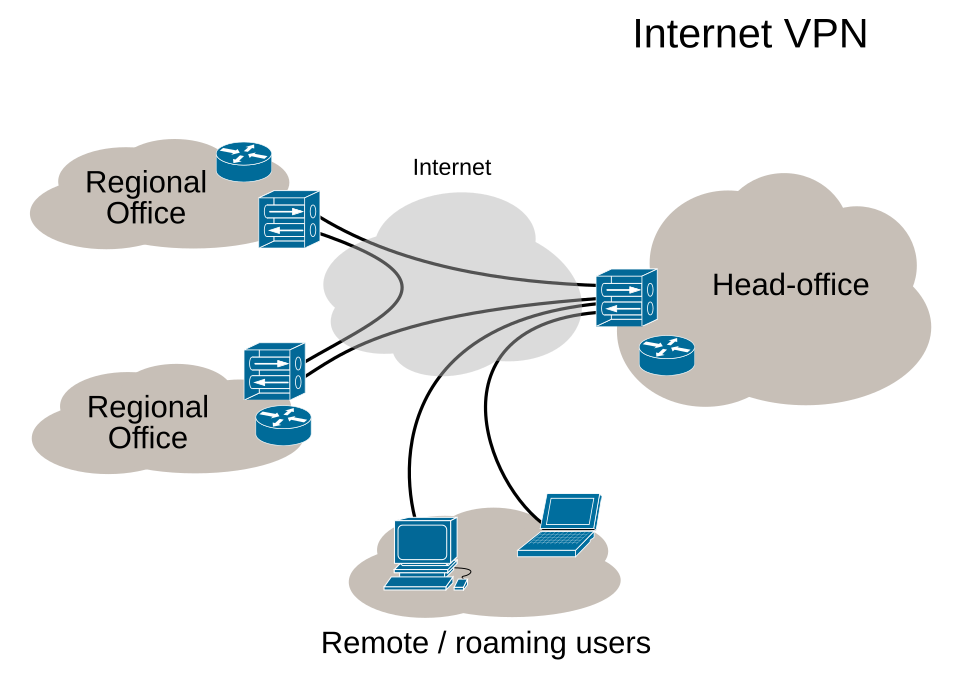
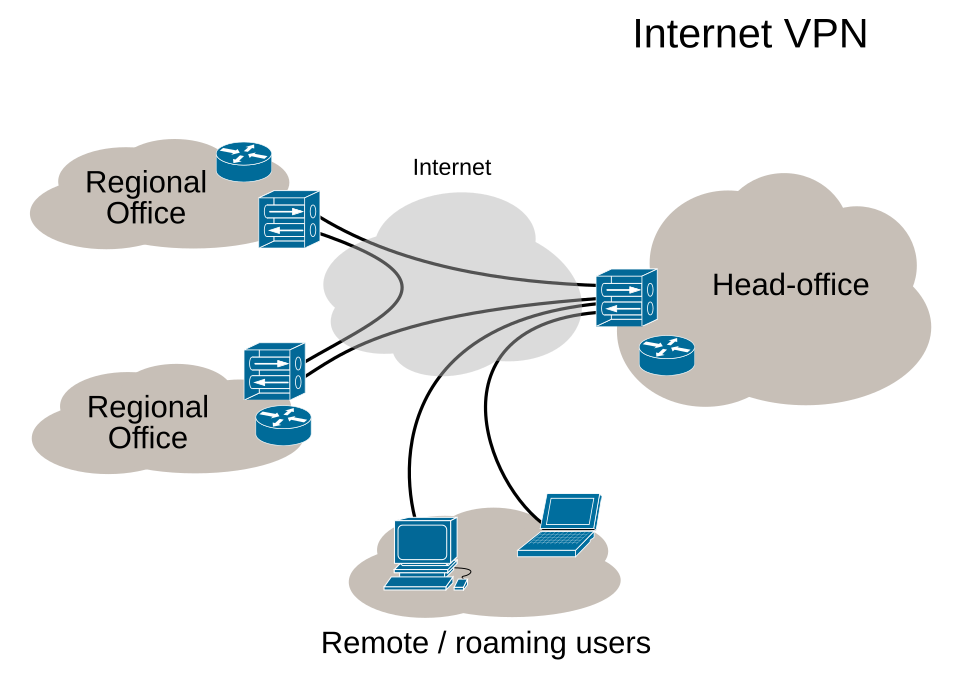
What you’ll find here: a steady stream of user-friendly content that covers five core areas: device reviews and usability for glucose monitors and insulin pumps; privacy and security for online health data, including VPN and data-protection tips; setup guides and how-tos for popular platforms and devices; price transparency and plan comparisons for digital health services; and country-specific considerations that matter to readers in different regions, including the United States and international markets. We avoid jargon and favor straightforward explanations, with concrete steps you can follow today.
Why this site exists: modern health management relies on reliable digital tools, secure online experiences, and clear pathways to actionable information. Diabetes Life exists to help people navigate these facets with confidence, tailoring guidance to practical use cases rather than theoretical best practices. Our content is crafted to support real-life decisions, whether you’re evaluating a new continuous glucose monitor (CGM) app, choosing a streaming solution for education videos, or configuring a home network to support telemedicine sessions.
How coverage is organized: content is organized around real-world tasks and needs. The home page highlights recent and relevant topical clusters, including:
- Device and tool reviews for CGMs, insulin pumps, smartphone apps, and companion wearables, with an emphasis on user experience, reliability, and price.
- Security and privacy guidance for protecting personal health information online, including VPN setup, data encryption practices, and best practices for safe cloud storage.
- How-to guides that walk readers through common tasks across Windows, macOS, iOS, Android, and smart home ecosystems—covering integration with health apps, cloud backups, and remote monitoring setups.
- Pricing and plans comparisons for digital health services, streaming platforms for health education, and privacy tools, with local currency references when relevant and practical.
- Country-specific considerations that reflect regulatory landscapes, local service availability, and commonly used payment methods to ensure guidance remains actionable for US readers and a broad international audience.
What makes our approach distinctive: we prioritize clarity, verifiable information, and independence. Our reviews are not sponsored by the brands named; when we reference the broader ecosystem, we do so with a neutral, evidence-based lens. For readers who want to understand how digital tools intersect with health management, we provide a transparent view of advantages, trade-offs, and practical setup steps.
How to use this home page: skim the top posts for trending topics, then drill into sections that match your current needs. You’ll see content that ranges from step-by-step setup guides to fast-read product summaries. The layout is designed for quick access to what matters most, whether you’re establishing a secure home network to support telehealth, evaluating a new mobile app for glucose logging, or comparing subscription options for digital education content related to diabetes management.
Local context you’ll notice: while the core guidance is universal, we include country-specific angles when relevant. For example, you’ll find notes on payment methods like credit cards, PayPal, or local equivalents in the United States and other regions; references to widely used devices such as Dexcom CGMs or Medtronic pumps; and considerations tied to privacy regulators and telemedicine norms in the US and beyond. We also highlight how local internet service providers and streaming platforms intersect with health education content, so you can plan a practical setup for streaming instructional videos, attending telehealth sessions, or accessing patient portals from home.
Comparing popular tools at a glance: this section is designed to help readers weigh options quickly. The following table summarizes a few well-known VPN and privacy tools commonly used to protect health data during online activity, along with typical price points in USD and basic feature notes. Prices are approximate and can vary by plan and promotions.
| Service | Typical Plan | Approx. Monthly Price (USD) | Key Features |
|---|---|---|---|
| NordVPN | Standard, Plus, Team | $11.95–$13.99 | Strong encryption, no-logs policy, wide server network, specialized servers for streaming |
| ExpressVPN | Monthly, 6-month, 12-month | $12.95–$24.95 | High-speed performance, user-friendly apps, reliable privacy protections |
| ProtonVPN | Free, Basic, Plus, Visionary | $0–$15.00+ | Strong security focus, transparent privacy stance, Router support |
Important note: prices and features can change. Always verify current plans and terms on the service’s site before purchasing. We aim to reflect practical costs and availability that matter to a household managing diabetes data and education needs.
Real-world anchors you’ll encounter: across the site, you’ll see references tied to concrete contexts—such as the use of Dexcom or FreeStyle Libre data in health apps, the role of telemedicine platforms in the US and EU, and the integration of streaming services for diabetes education videos. Local details such as the availability of devices in the US, regional privacy rules, and payment methods in different markets help ensure that guidance remains grounded and actionable beyond generic advice.
Navigation tips: the homepage emphasizes quick access to top posts, but you’ll also discover deeper dives into: setup workflows for Windows, macOS, iOS, and Android; tips for maintaining privacy while streaming medical education; and buyer’s guides that compare features, warranties, and support options. Each section uses practical, step-by-step instructions designed for immediate use in daily life, from arranging a secure home network for telehealth to configuring streaming devices for reliable education content.
- VPNs
Ultrasurf vpn edge: comprehensive guide to features, setup, safety, performance, and alternatives for 2025
Tobias Pestana · March 7, 2026 - VPNs
Super vpn owner guide: best VPN for privacy, streaming, security, and remote work in 2025
Yuki Jovanovic · March 7, 2026 - VPNs
Why does vpn automatically turn on and how to control auto-connect on Windows macOS iOS and Android
Oliver Dahlgren · March 7, 2026
Recent in other languages
Latest posts across 18 languages
- How to Completely Delete ProtonVPN from Your MacBook (ZA) – A Simple, Step‑By‑Step Guide to Uninstalling ProtonVPN Fully
- Nordvpn cost in south africa your full breakdown 2026: NordVPN South Africa pricing, plans, and value in 2026
- How to See and Manage Devices Connected to Your NordVPN Account: Quick Guide, Tips, and Best Practices